Terms of engagement: US computer crime laws out of step with changing attitudes to pen tests, ethical hacking | The Daily Swig
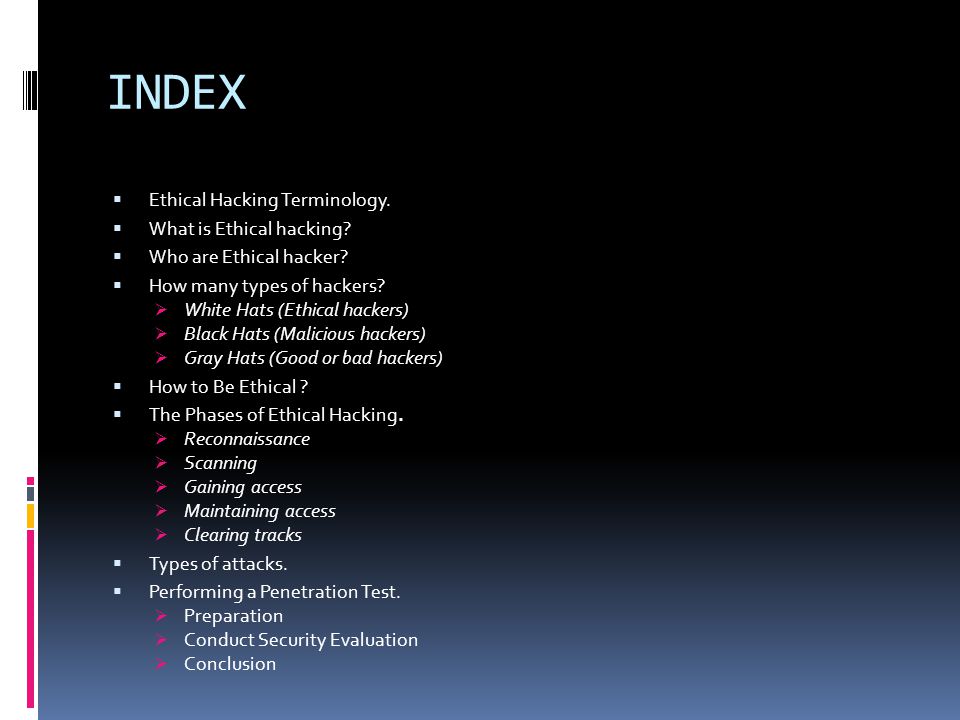
INDEX Ethical Hacking Terminology. What is Ethical hacking? Who are Ethical hacker? How many types of hackers? White Hats (Ethical hackers) - ppt download
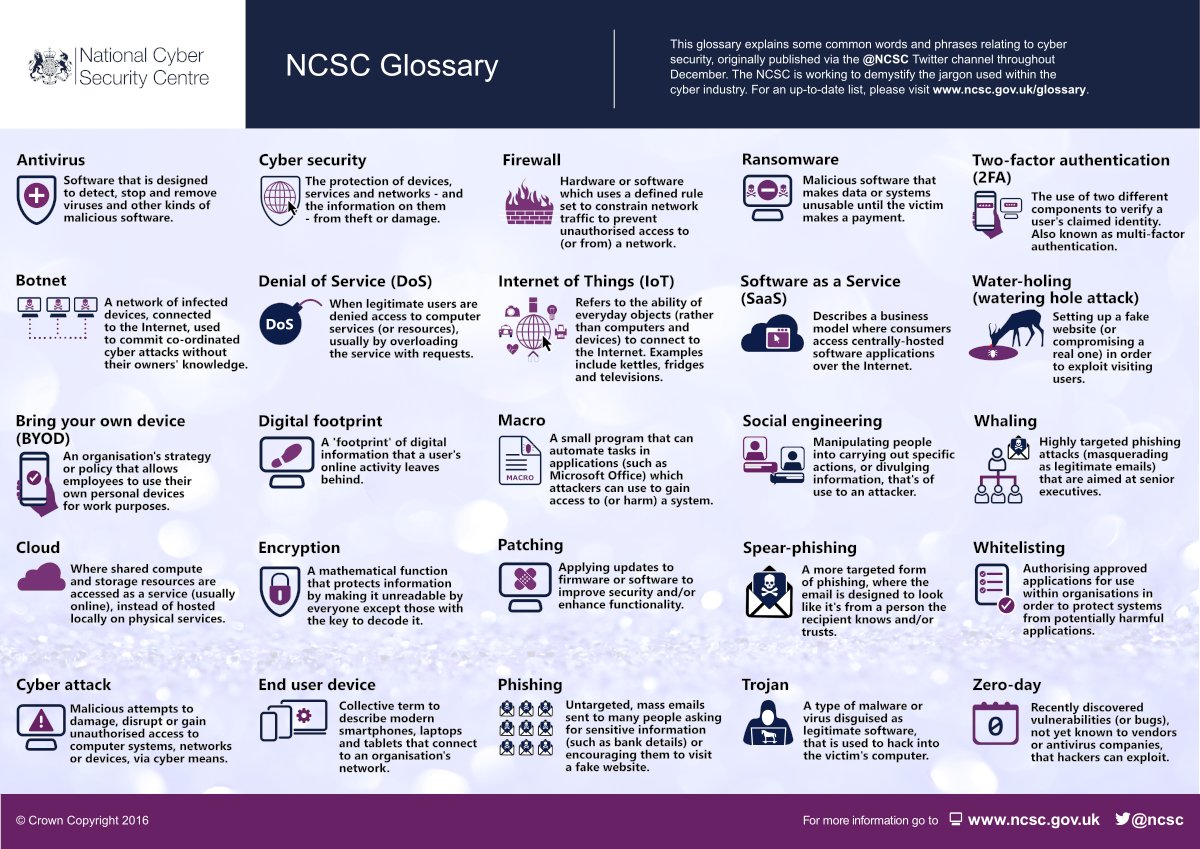
DSN auf Twitter: „#Ciberseguridad Glosario @NCSC➡️Definiciones directas para términos comunes de seguridad cibernética➡️Hacked or hooked? Check out our glossary for the meanings of some common cyber terms https://t.co/bnBzykep5G https://t.co ...

Hackers and their vocabulary Threats and risks Types of hackers Gaining access Intrusion detection and prevention Legal and ethical issues HACKING CLICKTECHSOLUTION.COM. - ppt download

Hacker Over A Screen With Binary Code Surrounded By Hacking Colorful Hacking Terms And Words Stock Photo, Picture And Royalty Free Image. Image 78947965.

Hacker Using Laptop. Hacking the Internet and Information Security Terms Cyber Security Concept Stock Photo - Image of business, cyber: 171284356

Computer Hacking Words Shows Data Stolen 3d Illustration Stock Illustration - Illustration of internet, hacker: 114611879
How to Hack Databases: The Terms & Technologies You Need to Know Before Getting Started « Null Byte :: WonderHowTo

![45 Ethical Hacking Terminologies that Sound Geeky [2023] 45 Ethical Hacking Terminologies that Sound Geeky [2023]](https://i0.wp.com/onlinecourseing.com/wp-content/uploads/2021/02/Ethical-Hacking-Terminologies-That-Sound-Geeky-Complete.jpg)

.jpg)